Cybersecurity researchers have discovered a targeted operation against Ukraine that has been found leveraging a nearly seven-year-old flaw in Microsoft Office to...
An ongoing social engineering campaign is targeting software developers with bogus npm packages under the guise of a job interview to trick...
Several security vulnerabilities disclosed in Brocade SANnav storage area network (SAN) management application could be exploited to compromise susceptible appliances. The 18 flaws impact all versions...
In today's digital world, where connectivity is rules all, endpoints serve as the gateway to a business’s digital kingdom. And because of this, endpoints are...
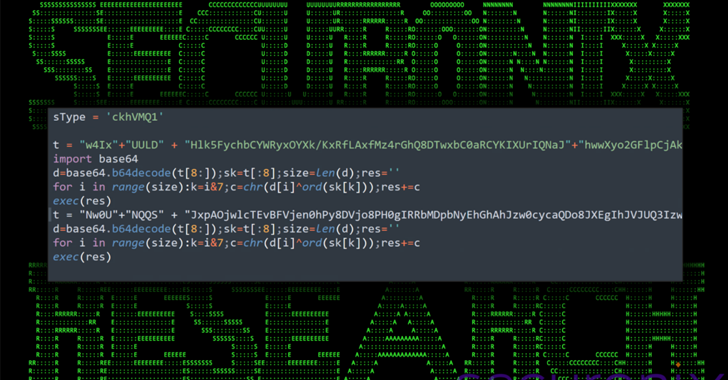
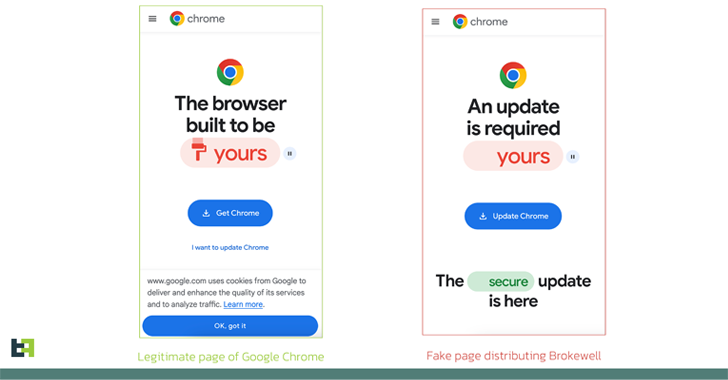
Fake browser updates are being used to push a previously undocumented Android malware called Brokewell. "Brokewell is a typical modern banking malware equipped...
Palo Alto Networks has shared remediation guidance for a recently disclosed critical security flaw impacting PAN-OS that has come under active exploitation. The vulnerability, tracked...
Threat actors are attempting to actively exploit a critical security flaw in the WP‑Automatic plugin for WordPress that could allow...
The North Korea-linked threat actor known as Lazarus Group employed its time-tested fabricated job lures to deliver a new remote access trojan...
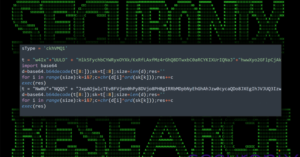
Follow this real-life network attack simulation, covering 6 steps from Initial Access to Data Exfiltration. See how attackers remain undetected with the simplest tools...
The U.S. Department of Justice (DoJ) on Wednesday announced the arrest of two co-founders of a cryptocurrency mixer called Samourai and seized the...