A previously undocumented "flexible" backdoor called Kapeka has been "sporadically" observed in cyber attacks targeting Eastern Europe, including Estonia and Ukraine, since...
The introduction of Open AI’s ChatGPT was a defining moment for the software industry, touching off a GenAI race with...
Threat actors are exploiting unpatched Atlassian servers to deploy a Linux variant of Cerber (aka C3RB3R) ransomware. The attacks leverage CVE-2023-22518 (CVSS...
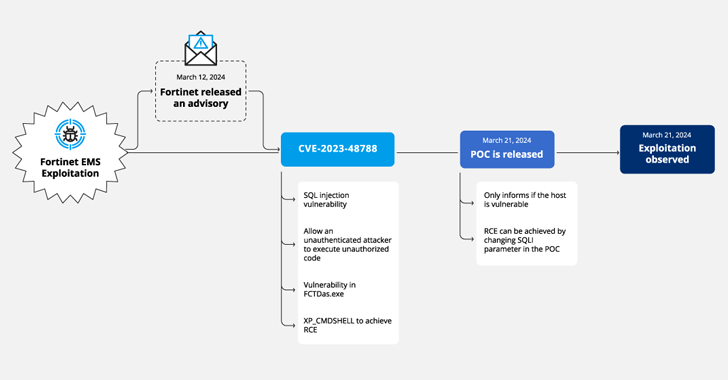
Cybersecurity researchers have discovered a new campaign that's exploiting a recently disclosed security flaw in Fortinet FortiClient EMS devices to...
Cisco is warning about a global surge in brute-force attacks targeting various devices, including Virtual Private Network (VPN) services, web...
Security researchers have uncovered a "credible" takeover attempt targeting the OpenJS Foundation in a manner that evokes similarities to the...
The threat actor tracked as TA558 has been observed leveraging steganography as an obfuscation technique to deliver a wide range of malware...
New cybersecurity research has found that command-line interface (CLI) tools from Amazon Web Services (AWS) and Google Cloud can expose...
The maintainers of the PuTTY Secure Shell (SSH) and Telnet client are alerting users of a critical vulnerability impacting versions from 0.68...
In today's rapidly evolving digital landscape, organizations face an increasingly complex array of cybersecurity threats. The proliferation of cloud services...