As we thread deeper into the digital age, a robust home Wi-Fi network has become more than a convenience; it’s...
Unveiling the Mystery: What is The Genius Wave? At the heart of many success stories lately is The Genius Wave,...
In the world of lottery games, winning big has always been a dream for many, but often seemed like an...
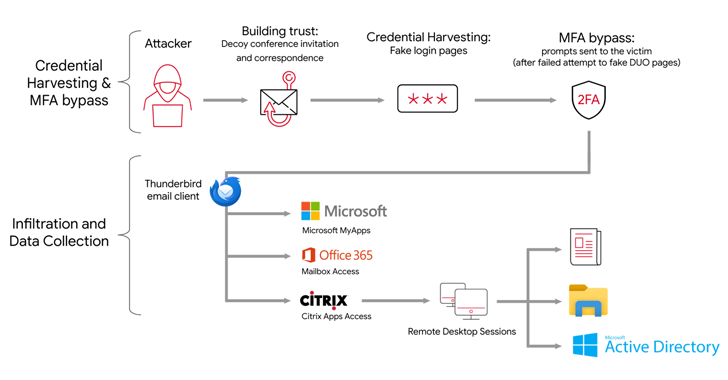
The Iranian state-backed hacking outfit called APT42 is making use of enhanced social engineering schemes to infiltrate target networks and cloud environments. Targets of...
The MITRE Corporation has offered more details into the recently disclosed cyber attack, stating that the first evidence of the...
How safe is your comments section? Discover how a seemingly innocent 'thank you' comment on a product page concealed a...
Google on Monday announced that it's simplifying the process of enabling two-factor authentication (2FA) for users with personal and Workspace...
A Russian operator of a now-dismantled BTC-e cryptocurrency exchange has pleaded guilty to money laundering charges from 2011 to 2017. Alexander Vinnik,...
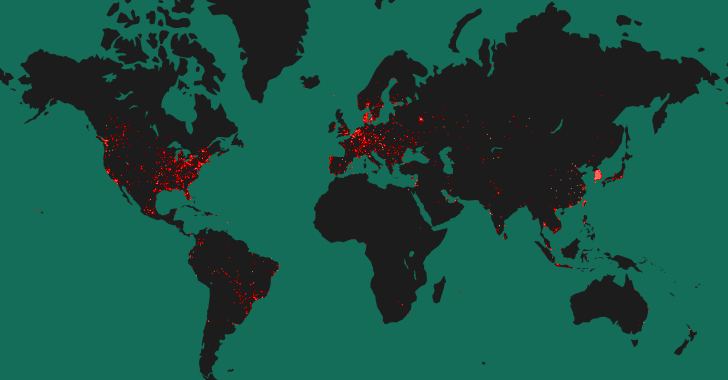
More than 50% of the 90,310 hosts have been found exposing a Tinyproxy service on the internet that's vulnerable to a critical...
The recently uncovered cyber espionage campaign targeting perimeter network devices from several vendors, including Cisco, may have been the work of...
Cybercriminals are vipers. They’re like snakes in the grass, hiding behind their keyboards, waiting to strike. And if you're a small-...
Multiple security vulnerabilities have been disclosed in various applications and system components within Xiaomi devices running Android. "The vulnerabilities in Xiaomi led...
Cybersecurity researchers have discovered a new information stealer targeting Apple macOS systems that's designed to set up persistence on the...