As we thread deeper into the digital age, a robust home Wi-Fi network has become more than a convenience; it’s...
Unveiling the Mystery: What is The Genius Wave? At the heart of many success stories lately is The Genius Wave,...
In the world of lottery games, winning big has always been a dream for many, but often seemed like an...
The North Korean threat actor tracked as Kimsuky has been observed deploying a previously undocumented Golang-based malware dubbed Durian as part of...
Artificial intelligence (AI) is transforming cybersecurity, and those leading the charge are using it to outsmart increasingly advanced cyber threats....
Google on Thursday released security updates to address a zero-day flaw in Chrome that it said has been actively exploited...
A guide to finding the right endpoint detection and response (EDR) solution for your business’ unique needs. Cybersecurity has become an ongoing...
Malicious Android apps masquerading as Google, Instagram, Snapchat, WhatsApp, and X (formerly Twitter) have been observed to steal users' credentials...
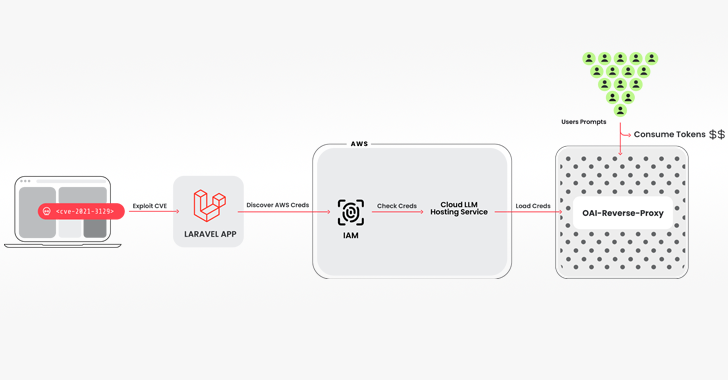
Cybersecurity researchers have discovered a novel attack that employs stolen cloud credentials to target cloud-hosted large language model (LLM) services with...
Researchers have detailed a Virtual Private Network (VPN) bypass technique dubbed TunnelVision that allows threat actors to snoop on victim's network traffic...
Polish government institutions have been targeted as part of a large-scale malware campaign orchestrated by a Russia-linked nation-state actor called APT28....
Cybersecurity and compliance guidance are in high demand among SMEs. However, many of them cannot afford to hire a full-time...
Two recently disclosed security flaws in Ivanti Connect Secure (ICS) devices are being exploited to deploy the infamous Mirai botnet. That's...