As we thread deeper into the digital age, a robust home Wi-Fi network has become more than a convenience; it’s...
Unveiling the Mystery: What is The Genius Wave? At the heart of many success stories lately is The Genius Wave,...
In the world of lottery games, winning big has always been a dream for many, but often seemed like an...
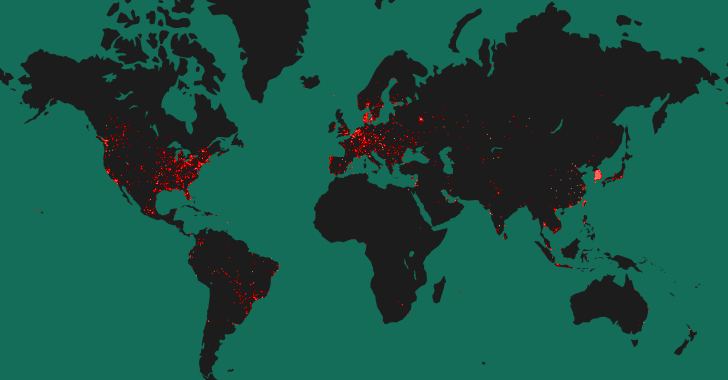
More than 50% of the 90,310 hosts have been found exposing a Tinyproxy service on the internet that's vulnerable to a critical...
The recently uncovered cyber espionage campaign targeting perimeter network devices from several vendors, including Cisco, may have been the work of...
Cybercriminals are vipers. They’re like snakes in the grass, hiding behind their keyboards, waiting to strike. And if you're a small-...
Multiple security vulnerabilities have been disclosed in various applications and system components within Xiaomi devices running Android. "The vulnerabilities in Xiaomi led...
Cybersecurity researchers have discovered a new information stealer targeting Apple macOS systems that's designed to set up persistence on the...
Czechia and Germany on Friday revealed that they were the target of a long-term cyber espionage campaign conducted by the...
In today's rapidly evolving digital landscape, the threat of Distributed Denial of Service (DDoS) attacks looms more significant than ever....
Threat actors have been increasingly weaponizing Microsoft Graph API for malicious purposes with the aim of evading detection. This is done to "facilitate communications with command-and-control...
SaaS applications are dominating the corporate landscape. Their increased use enables organizations to push the boundaries of technology and business. At...
The U.S. government on Thursday published a new cybersecurity advisory warning of North Korean threat actors' attempts to send emails in...