Between crossovers - Do threat actors play dirty or desperate? In our dataset of over 11,000 victim organizations that have...
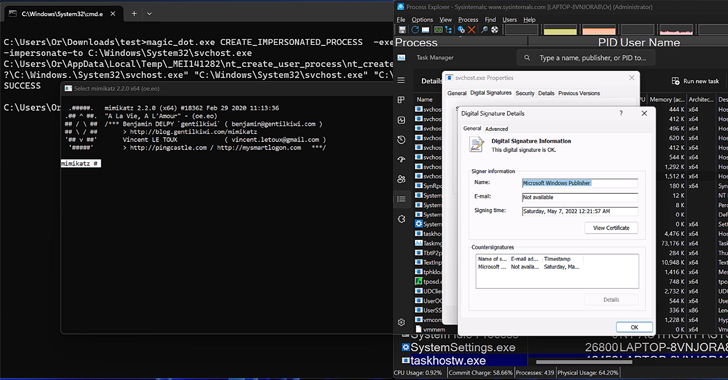
New research has found that the DOS-to-NT path conversion process could be exploited by threat actors to achieve rootkit-like capabilities...
Microsoft has revealed that North Korea-linked state-sponsored cyber actors has begun to use artificial intelligence (AI) to make its operations...
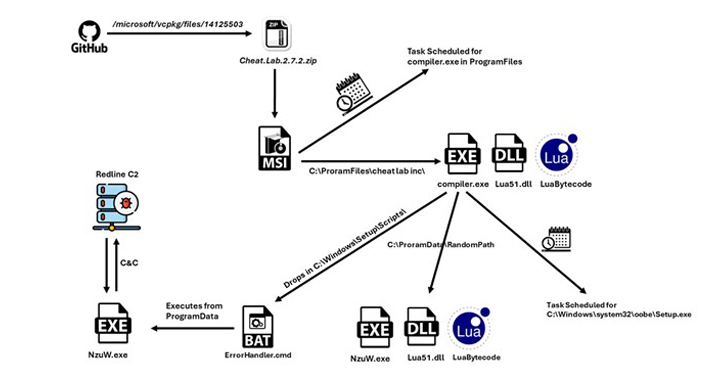
A new information stealer has been found leveraging Lua bytecode for added stealth and sophistication, findings from McAfee Labs reveal....
Palo Alto Networks has shared more details of a critical security flaw impacting PAN-OS that has come under active exploitation in the...
Users of the CrushFTP enterprise file transfer software are being urged to update to the latest version following the discovery of a security flaw that...
Technology, research, and government sectors in the Asia-Pacific region have been targeted by a threat actor called BlackTech as part of a recent...
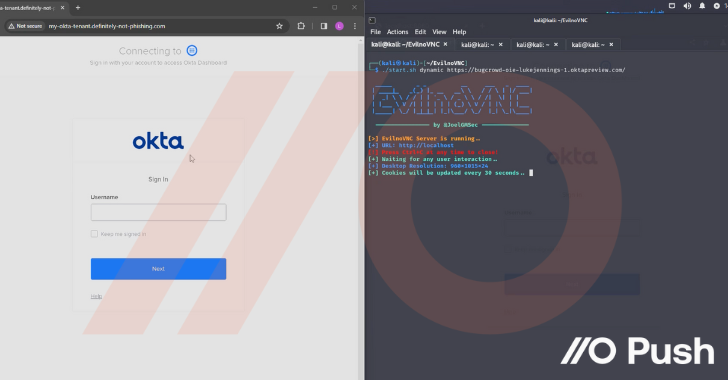
Attackers are increasingly making use of “networkless” attack techniques targeting cloud apps and identities. Here’s how attackers can (and are) compromising organizations – without ever needing...
Threat actors behind the Akira ransomware group have extorted approximately $42 million in illicit proceeds after breaching the networks of...
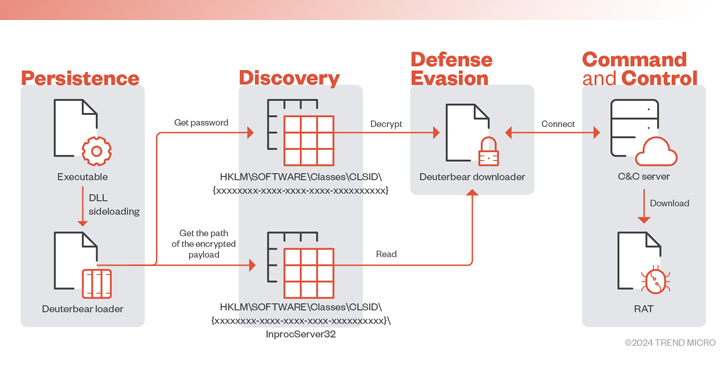
Government entities in the Middle East have been targeted as part of a previously undocumented campaign to deliver a new backdoor dubbed...