The infamous cybercrime syndicate known as FIN7 has been linked to a spear-phishing campaign targeting the U.S. automotive industry to...
Super Low RPO with Continuous Data Protection:Dial Back to Just Seconds Before an Attack Zerto, a Hewlett Packard Enterprise company,...
Sandboxes are synonymous with dynamic malware analysis. They help to execute malicious files in a safe virtual environment and observe...
A new Android trojan called SoumniBot has been detected in the wild targeting users in South Korea by leveraging weaknesses in the...
As many as 37 individuals have been arrested as part of an international crackdown on a cybercrime service called LabHost that has...
Threat actors are actively exploiting critical vulnerabilities in OpenMetadata to gain unauthorized access to Kubernetes workloads and leverage them for...
A new Google malvertising campaign is leveraging a cluster of domains mimicking a legitimate IP scanner software to deliver a...
A previously undocumented "flexible" backdoor called Kapeka has been "sporadically" observed in cyber attacks targeting Eastern Europe, including Estonia and Ukraine, since...
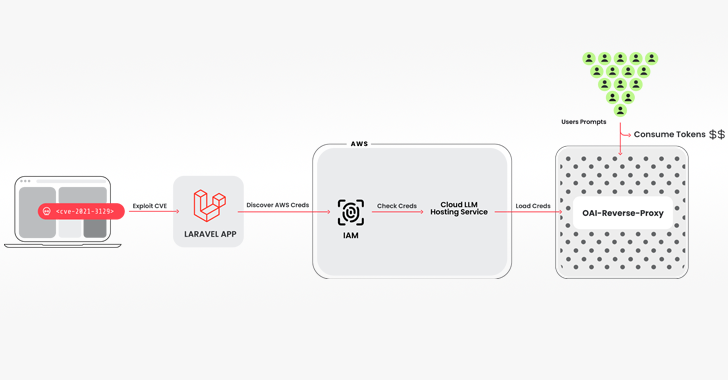
The introduction of Open AI’s ChatGPT was a defining moment for the software industry, touching off a GenAI race with...
Threat actors are exploiting unpatched Atlassian servers to deploy a Linux variant of Cerber (aka C3RB3R) ransomware. The attacks leverage CVE-2023-22518 (CVSS...