Technology, research, and government sectors in the Asia-Pacific region have been targeted by a threat actor called BlackTech as part of a recent...
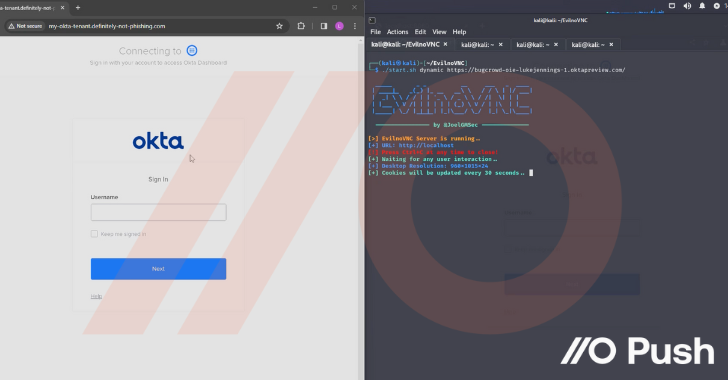
Attackers are increasingly making use of “networkless” attack techniques targeting cloud apps and identities. Here’s how attackers can (and are) compromising organizations – without ever needing...
Threat actors behind the Akira ransomware group have extorted approximately $42 million in illicit proceeds after breaching the networks of...
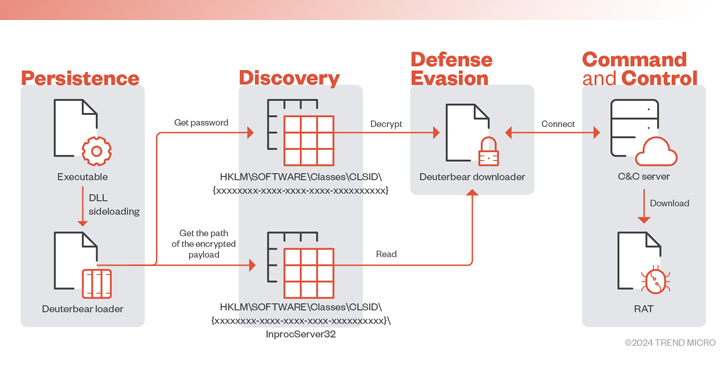
Government entities in the Middle East have been targeted as part of a previously undocumented campaign to deliver a new backdoor dubbed...
Select Ukrainian government networks have remained infected with a malware called OfflRouter since 2015. Cisco Talos said its findings are...
The infamous cybercrime syndicate known as FIN7 has been linked to a spear-phishing campaign targeting the U.S. automotive industry to...
Super Low RPO with Continuous Data Protection:Dial Back to Just Seconds Before an Attack Zerto, a Hewlett Packard Enterprise company,...
Sandboxes are synonymous with dynamic malware analysis. They help to execute malicious files in a safe virtual environment and observe...
A new Android trojan called SoumniBot has been detected in the wild targeting users in South Korea by leveraging weaknesses in the...
As many as 37 individuals have been arrested as part of an international crackdown on a cybercrime service called LabHost that has...